Attribution mapper: Visualize connections between threats and their sources
Use attribution mapper to analyze malware, identify threats, and streamline reporting for better cybersecurity decisions.

Similar apps
Uncover threat connections with ease
Visualize the origins of malware threats effortlessly
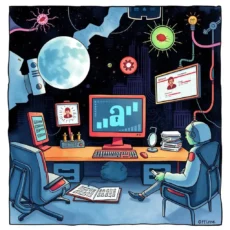
Comprehensive input fields for enhanced analysis
Our app provides multiple form fields for users to enter essential data such as malware sample names, hashes, analysis dates, and more. This thorough collection of inputs ensures that you never miss vital information, leading to a more holistic understanding of threat connections.
Detailed output results tailored for analysts
After processing the data through our advanced LLM, users receive precise output that illuminates the relationship between malware threats and their sources. This feature empowers Threat Intelligence Analysts and Cyber Threat Researchers to make informed decisions based on comprehensive insights.

User-friendly interface designed for security experts
Our web app is designed with ease-of-use in mind. The intuitive layout allows Malware Analysts and Incident Response Specialists to efficiently navigate through input forms, reducing time spent on data entry and enhancing productivity in threat attribution tasks.

Robust data collection for in-depth insights
Using fields like observed behaviors of malware and indicators of compromise (IOCs), our tool facilitates a rich understanding of malware functionality. Collecting this data enables threat attribution specialists to perform in-depth analysis, linking threats back to their origins with confidence.

Flexibility to document related sources seamlessly
Users can easily enter related threat reports or sources alongside their initial findings. This built-in feature supports comprehensive documentation efforts, allowing Cyber Threat Researchers to connect various pieces of intelligence and produce detailed reports effortlessly.

Space for additional comments enhancing contextual understanding
The inclusion of a comments field enables analysts to add personal insights or contextual information that may not fit into predefined categories. This flexibility allows for richer discussions within your team regarding each malware case and enhances collaborative efforts in threat attribution.
Additional information
Best for: Threat Intelligence Analyst, Malware Threat Researcher, Threat Attribution Specialist, Cyber Threat Analyst, Malware Attribution Analyst