Endpoint incident report generator: Generate incident reports based on endpoint data
Easily document security incidents with the endpoint incident report generator. Capture vital details, streamline analysis, and enhance incident response.
Similar apps
Effortless incident reporting
Streamline your threat hunting process
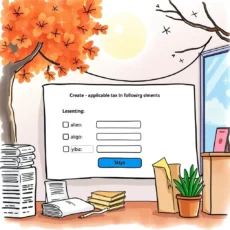
Comprehensive data input fields
Our app features multiple input fields that guide users to enter crucial information, such as incident date, endpoint identifier, and types of threats. This structured approach ensures that no important detail is overlooked, enabling your team to conduct thorough incident investigations.

Clear and concise output generation
Once all data is provided, our advanced LLM processes the text and formulates a well-structured incident report. The generated output is clear and concise, making it easy for your team to understand the situation quickly and take appropriate actions.

Customizable information capture
Each input field can be tailored to capture specific details relevant to your unique incidents. Whether it's user actions taken or specific evidence logs, our tool allows flexibility in documenting critical information accurately for future analysis.

Enhanced communication with stakeholders
Utilizing our incident report generator facilitates improved communication with stakeholders. The app's clear output ensures that all necessary information is presented effectively for quick reviews during security meetings or audits.

Improved accountability in incident response
By documenting every aspect of an incident through diverse input options, you'll create accountability among team members. The generated reports serve as official records that can be referenced in future investigations or compliance audits.
Additional information
Best for: Threat Hunting Analyst, Endpoint Security Analyst, Incident Response Analyst, Cybersecurity Incident Handler, Threat Intelligence Specialist